Google Chrome Browser Hacked, But No Details on How Yet
Google has been touting how secure Chrome is, and has had a challenge out there for a while to take it on, well somebody did find a way!
Google Chrome Browser Cracked by Security Researchers
“A team of security experts at Vupen Security, a specialist in vulnerability research for defensive and offensive security, claimed they have successfully cracked Google’s Chrome browser and its sandbox, denting Google’s claim that its browser is as secure as the company says. A video on Vupen’sWeb site shows the exploit in action with Google Chrome v11.0.696.65 on Microsoft Windows 7 SP1 (x64). The user is tricked into visiting a specially crafted web page hosting the exploit, which will execute various payloads to ultimately download the Calculator from a remote location and launch it outside the sandbox (at Medium integrity level).
For security reasons, the exploit code and technical details of the underlying vulnerabilities will not be publicly disclosed, the security team said in a post on their Web site, and noted they are exclusively shared with their government customers as part of their vulnerability research services. Vupen also disclosed the exploit works on both Chrome versions 11.x and 12.x. It was tested with Chrome v11.0.696.65 and v12.0.742.30.
‘The exploit shown in this video is one of the most sophisticated codes we have seen and created so far as it bypasses all security features including ASLR/DEP/Sandbox (and without exploiting a Windows kernel vulnerability), it is silent (no crash after executing the payload), it relies on undisclosed (0day) vulnerabilities discovered by Vupen and it works on all Windows systems (32-bit and x64),’ the Vupen Vulnerability Research Team wrote in the post. ‘While Chrome has one of the most secure sandboxes and has always survived the Pwn2Own contest during the last three years, we have now uncovered a reliable way to execute arbitrary code on any default installation of Chrome despite its sandbox, ASLR and DEP.'”
Of course, this just means that Google will “harden it” even more, and I think it will remain the most secure browser out there!
 As you know, backing up your computer is extremely important! If you don’t backup your critical files, you will lose them, because all computer hardware will fail at some point! So, the question is, how do you do backups? You can backup to tape, or you can backup to another computer that you have locally, but that requires additional hardware, and it requires lot’s of effort to set up and administer, AND you have to remember to do it, or, in some way automate it with scripts.
As you know, backing up your computer is extremely important! If you don’t backup your critical files, you will lose them, because all computer hardware will fail at some point! So, the question is, how do you do backups? You can backup to tape, or you can backup to another computer that you have locally, but that requires additional hardware, and it requires lot’s of effort to set up and administer, AND you have to remember to do it, or, in some way automate it with scripts.



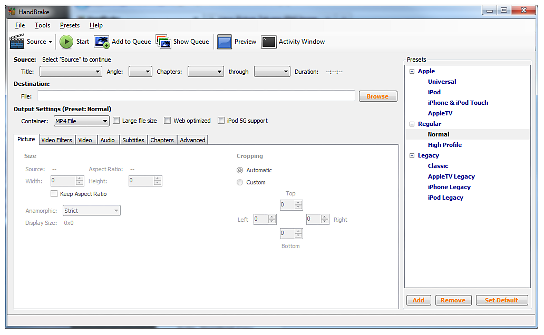 This week’s GSotW goes highly recommended by the aforementioned Patrick Norton, and his cohort on HD Nation on Revision3, Robert Heron! Handbrake is “yet another” video transcoder tool. But, it is free, Open Source, and has lot’s of neat features!
This week’s GSotW goes highly recommended by the aforementioned Patrick Norton, and his cohort on HD Nation on Revision3, Robert Heron! Handbrake is “yet another” video transcoder tool. But, it is free, Open Source, and has lot’s of neat features!